Nine minutes. That is the number that broke crypto Twitter yesterday.
Google’s Quantum AI team published a whitepaper on March 31 stating that a sufficiently powerful quantum computer could crack a Bitcoin private key in roughly nine minutes once a public key is briefly exposed during a transaction. Bitcoin transactions typically take about ten minutes to confirm. The math is uncomfortable. An attacker with the right machine would beat the clock 41% of the time.
Quantum-resistant tokens jumped 50% overnight. Crypto forums filled with people asking whether their wallets were safe. Michael Saylor posted. Elon Musk joked that forgotten wallet passwords would be “accessible in the future.”
🚨 BREAKING
GOOGLE JUST RELEASED A NEW QUANTUM ALGORITHM DESIGNED TO HACK CRYPTO PRIVATE KEYS.
→ 13,000X FASTER THAN BEFORE
→ CAN HACK ANY WALLET IN 9 MINUTES
→ 41% SUCCESS RATETHIS IS NOT LOOKING GOOD FOR BITCOIN… pic.twitter.com/nBmdOIQ1AU
— 0xNobler (@CryptoNobler) March 31, 2026
Before you do anything with your holdings, it is worth reading what Google actually said and, more importantly, what it did not say.
The Research Is Real. The Machine Is Not
Google’s paper does something genuinely significant. It cuts the estimated computing resources needed to break Bitcoin’s elliptic curve cryptography by a factor of roughly 20. Previous estimates suggested breaking the encryption would require millions of quantum bits, or qubits, placing the threat comfortably in the distant future. Google’s new estimates put the threshold at under 500,000 physical qubits, with attacks requiring around 1,200 to 1,450 high-quality logical qubits.
That is meaningfully closer than the field previously assumed. The paper is co-authored by Google researchers, Ethereum Foundation researcher Justin Drake, and Stanford cryptographer Dan Boneh. These are serious people publishing serious work.
But Google also states clearly: no such machine exists today. The most advanced quantum systems in operation are not close to 500,000 physical qubits at the reliability levels needed for this kind of attack. The gap between current hardware and the attack threshold is still measured in years of engineering progress, not months.
What the paper actually changes is the timeline estimate and the urgency of preparation. It does not change the present-day risk to your Bitcoin wallet.
What Is Actually at Risk Right Now
The threat is not uniform across all Bitcoin holdings. The paper identifies three categories of attack, and they have very different practical implications.
The nine-minute attack, the one making headlines, applies to what researchers call an “on-spend” attack. When you send Bitcoin, your public key is briefly visible before the transaction confirms. A quantum attacker watching the mempool could, in theory, extract your private key during that window and redirect the funds. This requires a fast quantum system capable of completing the computation in under ten minutes.
The second category is an “at-rest” attack targeting wallets where the public key has already been permanently exposed. This includes anyone who has ever sent Bitcoin from an address, since sending reveals the public key, and anyone using older address formats that expose keys by default. About 6.9 million Bitcoin, roughly one-third of the total supply, already sit in wallets with exposed public keys. These are the most vulnerable holdings if quantum computing reaches the necessary scale.
The third category, “on-setup” attacks, targets protocol-level parameters in systems like Ethereum’s KZG trusted setup and Zcash’s Sapling protocol. These are infrastructure-level vulnerabilities that would require protocol upgrades rather than individual wallet changes.
Bitcoin’s proof-of-work mining mechanism, notably, is not vulnerable to this class of quantum attack. The threat is to digital signatures and wallet cryptography, not to the mining process itself.
Why Taproot Makes This More Complicated
One detail buried in the paper deserves more attention than it has received. Bitcoin’s Taproot upgrade, deployed in 2021, improved transaction efficiency and privacy by making public keys visible by default in a wider range of transaction types. That design choice, beneficial for most purposes, expands the pool of wallets potentially vulnerable to quantum attacks.
The paper does not suggest Taproot was a mistake. The benefits are real and the quantum threat was already understood when the upgrade was designed. But it does mean the population of wallets with exposed public keys is larger than it would be under older address formats, and the urgency of developing quantum-resistant alternatives is correspondingly higher.
BIP-360, the Bitcoin Improvement Proposal that would introduce post-quantum cryptographic standards for Bitcoin wallets, has been in development and is now getting significantly more attention. The timeline pressure Google just introduced makes that proposal considerably more urgent.
The Tokens Rallying 50% Are Not the Answer
Here is where the story gets worth examining carefully.
In the hours after Google’s paper dropped, a basket of tokens marketed as “quantum resistant” jumped 50%. These are smaller projects that have built their identity around post-quantum cryptography, positioning themselves as the safe alternative if Bitcoin’s encryption fails.
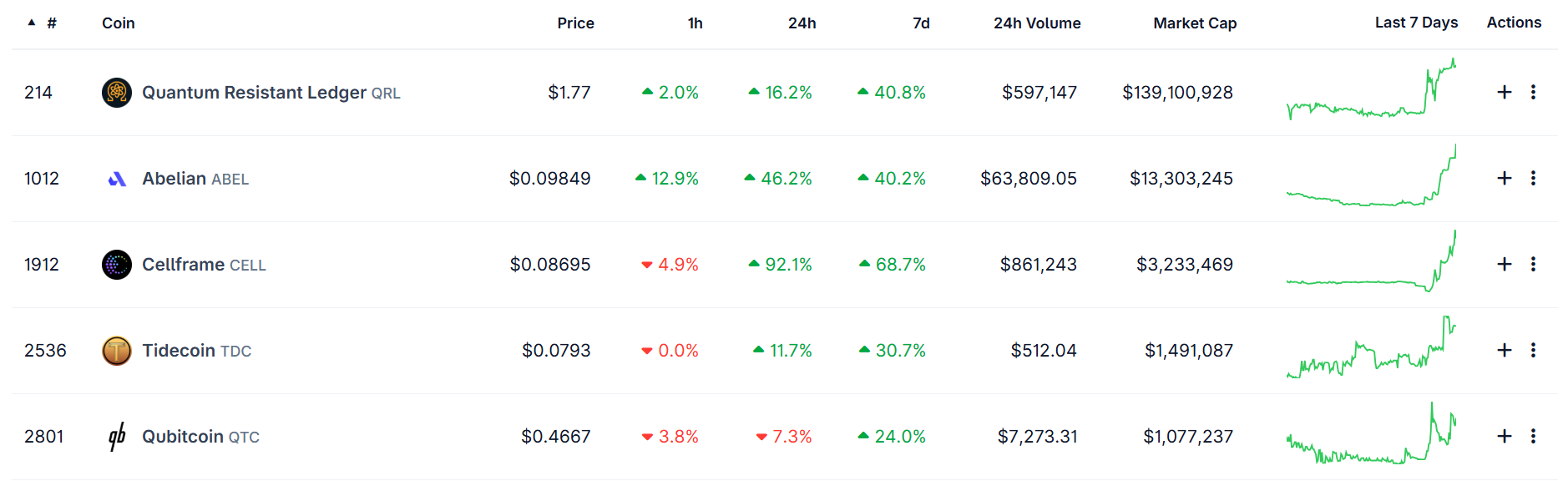
Quantum Resistant Coins Source: Coingecko
The 50% move is a market sentiment reaction, not a technical validation. Most of these projects face their own implementation challenges, have not been independently audited for quantum resistance at the level the threat demands, and carry the liquidity and counterparty risks typical of small-cap tokens. Buying a “quantum resistant” token as a hedge against quantum computing breaking Bitcoin is a bit like buying earthquake insurance from a company that has never paid a claim.
The actual post-quantum solution for Bitcoin is BIP-360 and the broader effort to migrate the protocol to post-quantum cryptographic standards. That work is happening inside Bitcoin’s development community, not in a token presale.
Justin Drake from the Ethereum Foundation put his personal probability of “Q-Day” by 2032 at 10% or higher. Haseeb Qureshi, managing partner at Dragonfly, called the threat “serious shit” and urged all blockchains to transition. Nic Carter compared the stakes to nuclear weapons development.
These are not people selling you a token. They are researchers and investors telling you the preparation window is real and it needs to start now.
The Counter-Argument Google’s Own Paper Makes
The most counterintuitive part of Google’s paper is that it also implicitly explains why Bitcoin is better positioned than most systems to respond.
Centralized systems, banks, governments, military networks, can push software updates to their users. The 2029 timeline Google has set for its own quantum-resistant migration is aggressive precisely because they control their own infrastructure. Bitcoin cannot do that. Protocol changes require community consensus, miner adoption, and a coordinated upgrade across thousands of independent nodes running in dozens of countries.
That sounds like a weakness. In some ways it is. The upgrade path is slower and more contested than any centralized institution faces.
But it is also why Bitcoin survived every previous threat, regulatory crackdowns, exchange collapses, mining bans, and market crashes. The same decentralized structure that makes quantum migration complex also makes Bitcoin impossible to shut down, censor, or unilaterally compromise. A quantum attacker could potentially steal from exposed wallets. They could not kill the network.
The more relevant question is whether the Bitcoin development community can coordinate a post-quantum migration before a cryptographically relevant quantum computer actually exists. CoinDesk reported that Ethereum has already launched an extensive post-quantum migration effort. Bitcoin’s community is moving more cautiously, as it tends to do, but BIP-360 is active and the conversation is now significantly more urgent.
What You Should Actually Do
For the vast majority of Bitcoin holders, the practical advice is simple and has not changed with this paper.
Do not reuse Bitcoin addresses. Each time you send from an address, you expose the public key. Using a fresh address for each transaction limits your exposure window. Most modern wallets handle this automatically.
Move holdings to a hardware wallet using modern address formats. Taproot addresses that expose public keys by default are more vulnerable than older formats like P2PKH for long-term storage purposes. This is a nuance, not an emergency.
Do not sell your Bitcoin to buy a 50% quantum token. That is a sentiment trade, not a security upgrade.
Watch BIP-360 development. The protocol-level solution is being built. When it is ready for adoption, upgrading will be the actual hedge.
The Honest Bottom Line
Google published important research. The timeline for quantum risk to Bitcoin is shorter than the field assumed. The specific number, nine minutes, is real under specific conditions that do not yet exist but may exist sooner than expected.
The threat is genuine enough that serious people who understand the technology are treating it seriously. It is not genuine enough to justify the 50% token rally that followed the paper’s release.
Bitcoin has survived everything the world has thrown at it for seventeen years. The quantum challenge is real, the preparation window is open, and the development community knows it. That is a different situation from being caught unprepared.
The nine-minute clock is not running yet. When it starts, the question is whether the upgrade work finished first.